What is layered security

Ava Arnold
Published Jan 01, 2026
What are the 3 layers of security?
basic layers – Deter, Delay, and Defend.- Deter. Deterring an attack means convincing possible intruders that they should seek a better target elsewhere. …
- Delay. The next goal is to delay any intruders. …
- Defense. The final layer is the one entirely too many think they should start with – defense.
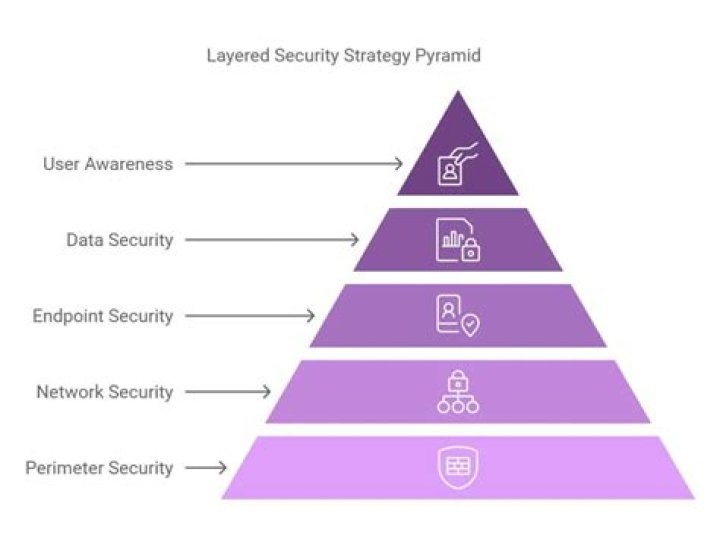
What are the 5 layers of security?
What are the 5 Layers of Security?- Active attacks. When an active attack occurs, the perpetrator is often trying to exploit any security loopholes to access and control your networks. …
- Passive attacks. …
- Solution perimeter security. …
- Network security. …
- Endpoint security. …
- Data security. …
- Security awareness training.
Why do we need layered security?
Objectives of Layered SecurityThe layered security approach that is widely used in today’s systems aims to ensure that each component of a system’s defense has as many backups as possible. These backups are designed to counter any possible security defects that could arise in the event of a sophisticated breach.
What are the 7 layers of security?
The OSI model’s seven layers are the: Human Layer, Perimeter Layer, Network Layer, Endpoint Layer, Application Layer, Data Layer, and Mission Critical Layer.What are the multiple layers of security?
Multiple Layers of Security- Secure Authentication.
- Firewalls and Perimeter Security.
- Data Encryption.
- Continuous Monitoring.
What is involved in a layered security plan?
The foundational component of layered security is perimeter defense, which involves keeping malicious traffic from ever reaching the network. Perimeter defense begins with a firewall, which can be implemented using software, a hardware appliance or a cloud-based solution.Who would review the organization’s layered approach to security?
The CISO (chief information security officer) would review the organizations layered approach to security. 9.What layers of security is successful to an organization?
5 Layers of Cybersecurity That Could Help Secure Your…- Physical. The physical layer of cybersecurity refers to your building, office or network closet. …
- Network. The network layer of cybersecurity refers to your wireless network, switches, firewalls, remote access, services and cloud services. …
- Devices. …
- People.
What properties of security controls provide layered security?
What properties of security controls provide layered security? Providing diversity of types of control and diversity of vendors from which controls are sourced. If a company wants to ensure it is following best practice in choosing security controls, what type of resource would provide guidance?What are the layers of physical security?
Businesses are constantly at risk of theft, particularly when their physical assets aren’t fully secure. The best way to keep thieves at bay is to break down security into four layers: deterrence, access control, detection and identification.What are the 6 layers of security?
Google shared a look in and around its data center by showcasing their 6-layers of security.- Layer 1: Signage and Fencing. …
- Layer 2: Secure Perimeter. …
- Layer 3: Building Access. …
- Layer 4: Security Operations Center. …
- Layer 5: Data Center Floor. …
- Layer 6: Secure Hard Drive Destruction. …
- Final Words.
How many layers of security are there?
The 7 Layers Of Cybersecurity.What is layered Defence strategy?
Using a layered approach when you plan your Internet security strategy ensures that an attacker who penetrates one layer of defense will be stopped by a subsequent layer. Your security strategy must include measures that provide protection across the following layers of the traditional network computing model.What is the difference between layered security and defense in depth?
Originally coined in a military context, the term “defense in depth” refers to an even more comprehensive security strategy approach than layered security. … A layered security solution also assumes a singular focus on the origins of threats, within some general or specific category of attack.How big is Google Serverroom?
The data centers are 250 feet long, 72 feet wide, 16 feet deep.Why is it important to have multiple layers of defense?
Many layers of securityProtecting information assets requires the combination of different information security technologies to create multiple layers of security in order to address a wide variety of security concerns. … Ultimately, they prevent attacks that originate from security flaws in web applications.



